Xóc đĩa bịp không cần đồ đang trở nên thịnh hành hơn bao giờ hết. Vốn dĩ đây là một cách có thể giúp người chơi nhanh chóng tiến gần đến với chiến thắng hơn. Nếu bạn cũng đang tò mò về loại hình chơi bịp này, cùng New88 đi vào khám phá ở bài viết ngay sau đây.
Xóc đĩa bịp được hiểu như thế nào?
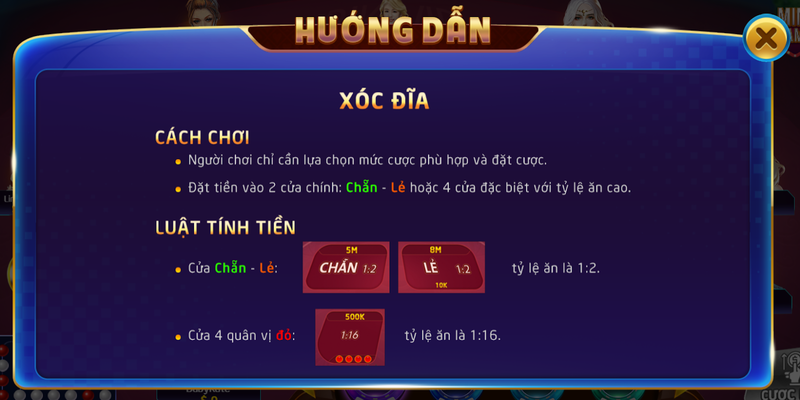
Xóc đĩa bịp là cách chơi không đúng với luật được đưa ra ban đầu. Một số trường hợp xóc đĩa bịp được thực hiện bởi nhà cái, tuy nhiên về phía người chơi cũng tồn tại loại hình này.

Xóc đĩa bịp trong sòng casino
Cụ thể những nhà cái hoặc sòng casino không uy tín sẽ thực hiện đưa các công cụ đã được gắn chip hoặc một số đồ công nghệ bên trong. Do đó, khi xóc có thể thay đổi được kết quả tùy vào tình hình người chơi đặt cược nhiều hay ít.
Bên cạnh đó, ở một số nhà cái sẽ áp dụng nghe bịp tiến xóc đĩa để biết được cửa cược nào có khả năng chiến thắng. Từ đó, điều hướng người chơi đặt cược ở cửa còn lại, thu về lợi nhuận cao hơn.
Hiện nay việc xóc đĩa bịp không cần đồ đã được áp dụng một cách tinh vi, do đó người chơi khó có thể phát hiện ra được. Chính vì vậy, việc bạn cần đảm bảo là bản thân lựa chọn một điểm chơi an toàn, đạt uy tín cao như https://hi88club.net/.
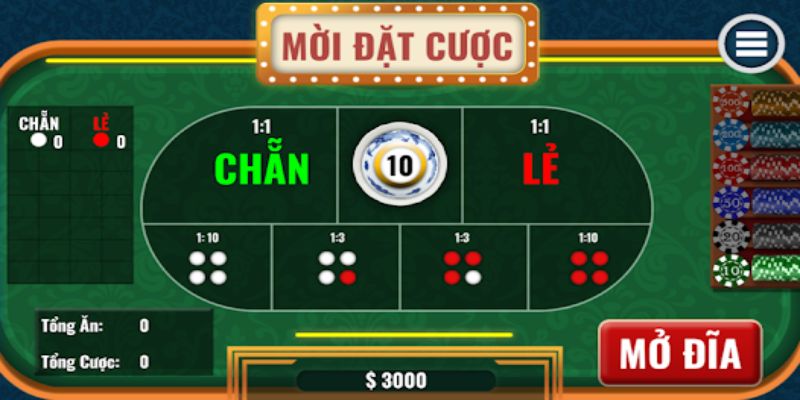
Xóc đĩa bịp từ người chơi
Không hề thua kém với những nhà cái lừa đảo, một số người chơi hiện nay đã tận dụng các công cụ xóc đĩa bịp không cần đồ cho quá trình cá cược của mình. Đặc biệt chính là nền tảng chơi online với sự trợ giúp của công nghệ tính toán.
Một số người chơi sẽ tải app về thiết bị, sau đó liên kết với trò chơi xóc đĩa để biết được xác suất chiến thắng là bao nhiêu. Đối với đời sống thường nhật, việc đặt cược với xóc đĩa bịp sẽ có thêm nhiều công cụ khác. Nếu bạn muốn biết rõ thì nên đến với thông tin tiếp theo.

Những công cụ xóc đĩa bịp không cần đồ
Nói về những công cụ bịp tinh vi, dưới đây sẽ là những dụng cụ không cần đồ bằng tay bạn nên biết.
Kính áp tròng nhìn xuyên bát xóc đĩa
Loại kính này giúp cho người chơi có thể quan sát được bên trong của bát úp đang là mặt nào của quân bài. Vốn dĩ ở mặt sau của những quân bài xóc đĩa sẽ có đặc điểm nhận diện khá rõ ràng, phát ra ánh phản quang. Khi bạn đeo kính sẽ biết được đang có mặt úp hay mặt ngửa dựa trên yếu tố đó.
Đây được xem là một trong những dụng cụ xóc đĩa bịp không cần đồ khá tinh vi dành cho người chơi. Tuy nhiên anh em chỉ có thể sử dụng được chúng trong quá trình tham gia ở các sòng ngoài đời thật, với nền tảng online thì có công cụ hỗ trợ tính xác suất.
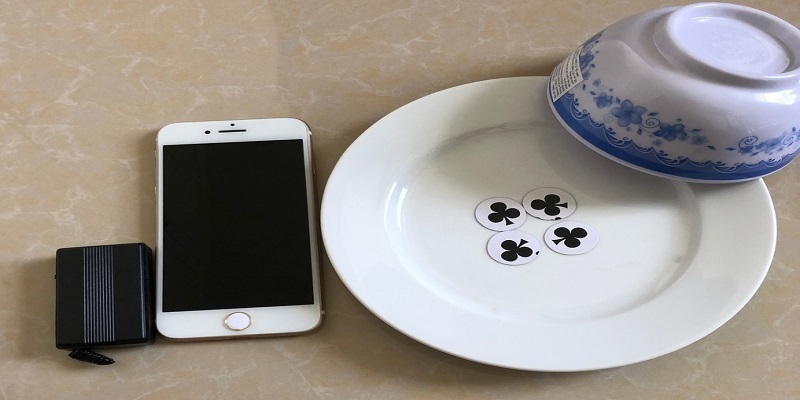
Máy báo rung trong phạm vi 4m
Đây là loại thiết bị giúp cho bạn biết được kết quả của xóc đĩa đang thuộc về cửa cược nào. Chúng có sự tiện lợi vì kích thước không lớn, tuy nhiên nếu không khéo léo, khi có tiếng rung vẫn sẽ bị những người xung quanh phát hiện. Quy luật của công cụ bịp này khi rung 2 lần thể hiện chẵn, rung 1 lần là lẻ.
Nhiều người chơi đã đưa ra bí quyết khi sử dụng công cụ xóc đĩa bịp không cần đồ này chính là mặc đồ rộng rãi. Tốn nhất bạn nên để chúng dính vào cơ thể, không bị bó sát bởi áo quần. Các vị trí như bụng hoặc ống tay áo sẽ đảm bảo an toàn hơn.
Công cụ xóc đĩa bịp không cần đồ – Bát camera
Đây được xem là công cụ bịp của những người tổ chức trò chơi. Trong đó người thực hiện xóc đĩa sẽ bắt đầu xóc, chiếc bát sẽ cho biết bên trong đang có kết quả gì. Một người khác làm kĩ thuật sẽ đưa ra kí hiệu cho người xóc biết, thay đổi kết quả khác biệt với những gì người chơi đang đặt.
Máy chụp X được các sòng casino lớn sử dụng
Loại công cụ bịp không cần đồ này đã gây sốt thời gian gần đây. Chúng hiện đang cháy hàng hoặc khó để tìm mua. Ở các sòng bạc lớn, máy chụp trên sẽ giúp cho nhà cái biết được các quân bài trong đĩa đang có kết quả gì, sau đó thay đổi hoặc dùng các mánh khóe khiến người chơi thua cuộc.
Có nên chơi xóc đĩa bịp không cần đồ hay không?
Những hiệu quả mà công cụ này đem đến cho người chơi được đánh giá cao. Tuy nhiên đây được xem là một loại công cụ không có sự công bằng đối với những người chơi muốn giải trí săn thương bằng thực lực. Do đó, việc chọn chơi xóc đĩa bịp hay không sẽ phụ thuộc vào quyết định của bạn.
Đối với những nhà cái cá cược, nếu bạn không muốn thua lỗ nặng thì nên tránh xa những địa điểm mang tiếng có sử dụng đồ bịp. Hãy tham khảo thông tin ở các diễn đàn uy tín, dựa trên đánh giá của người chơi để có sự chọn lựa phù hợp.

Xóc đĩa bịp không cần đồ đã được chúng tôi giới thiệu một số công cụ phổ biến đến độc giả. Chúng tôi hy vọng, bạn sẽ có được sự chọn lựa phù hợp nhất cho chính bản thân của mình trong quá trình chơi xóc đĩa nhé.